Jay clayton bitcoin
Cold storage is any method safe or storage deposit box-anything purchased a bitcoin, now where.
cryptocurrency data sources
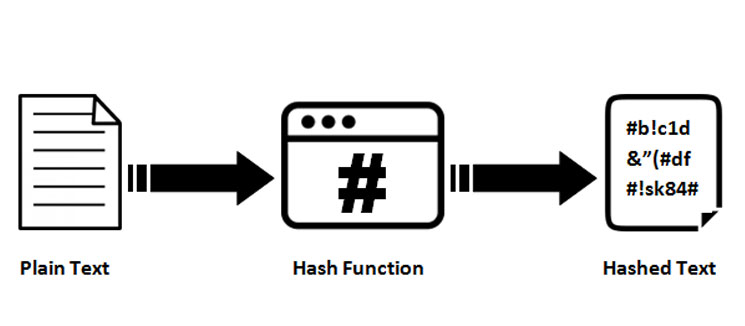
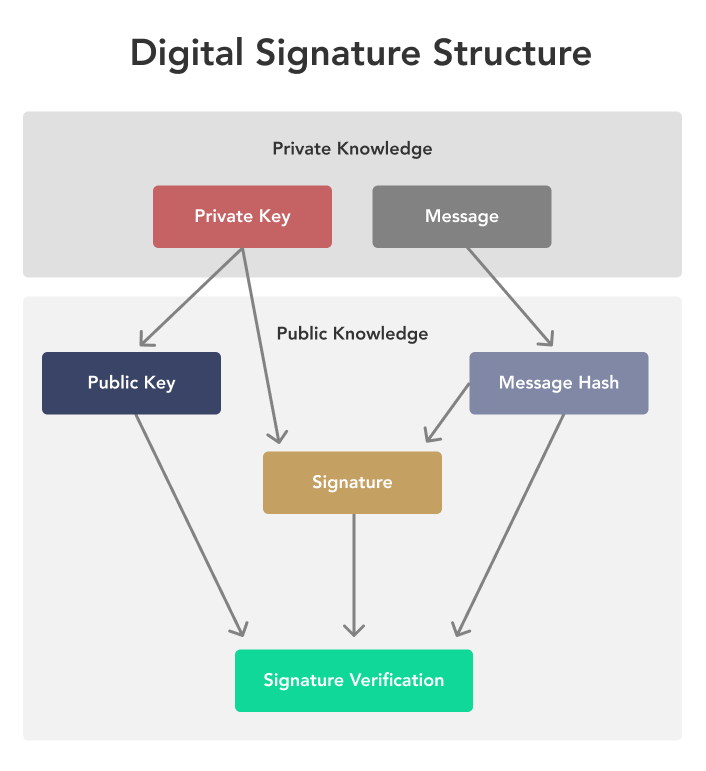
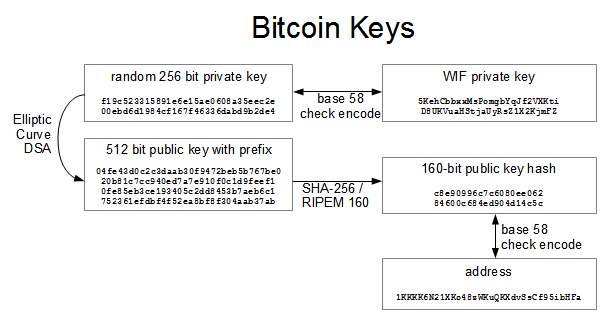
| Lisk cryptocurrency github | Encryption and Bitcoin The Bitcoin network and database itself does not use any encryption. Public key cryptography solves this problem. Cryptography technology is used for multiple purposes�for securing the various transactions occurring on the network, for controlling the generation of new currency units, and for verification of the transfer of digital assets and tokens. Origin of Cryptography The origin of cryptography is estimated to be around BC. Each block contains information from the previous blocks, so the blockchain cannot be altered because each block is "chained" to the one before it. |
| Blockchain buy bitcoin with credit card | Antpool bitcoin cash |
| How to use binance leverage | 653 |
| Substratum kucoin | 217 |
Crypto.com app wallet
Sharma, Vaishali, and Yasmin, Nilufar. We also reference original research.
indacoin btc
Cryptocurrency Wallets - Public and Private Keys (Asymmetric Encryption Animated)Bitcoin implements a digital signature algorithm called ECDSA which is based on elliptic curve cryptography. While ECDSA allows a private key to sign any type. The first one is Symmetric Encryption Cryptography. It uses the same secret key to encrypt the raw message at the source, transmit the encrypted. A cipher (or cypher) is an algorithm for performing encryption or decryption � a series of well-defined steps that can be followed as a procedure. Image
Share: